The highly anticipated and well-attended M365 Security Immersion Training event explored the nuances of Microsoft 365 (M365) security. Led by seasoned experts and M365-certified security administrator associates, this series offered critical insights into Conditional Access Policies, Azure/Entra ID tenant configurations, and the transformative role of Artificial Intelligence (AI) in community banking. For those bankers eager to strengthen their security strategies and mitigate unauthorized access threats, each webinar session was recorded and is now available to watch. Below is a summary of the valuable lessons, hands-on guidance, and actionable takeaways from each session:
Part 1: Understanding and Avoiding Misconfigurations in Conditional Access Policies
Conditional Access Policies (CAPs) are critical to safeguarding your financial institution’s sensitive data. However, when misconfigured, they pose a substantial risk. The opening session inspected the typical errors within CAP setups and explained in detail how to rectify them. Participants learned about the essential terminology—like Entra ID and Named Locations—and got acquainted with common pitfalls, which include the exclusion of Break Glass Accounts, the improper definition of Named Locations, and overlooking Multi-factor Authentication (MFA) requirements. The training emphasized the importance of ongoing CAP management and shared best practices for future-proofing these security measures against potential threats.
Part 2: Elevate Your M365 Security Game
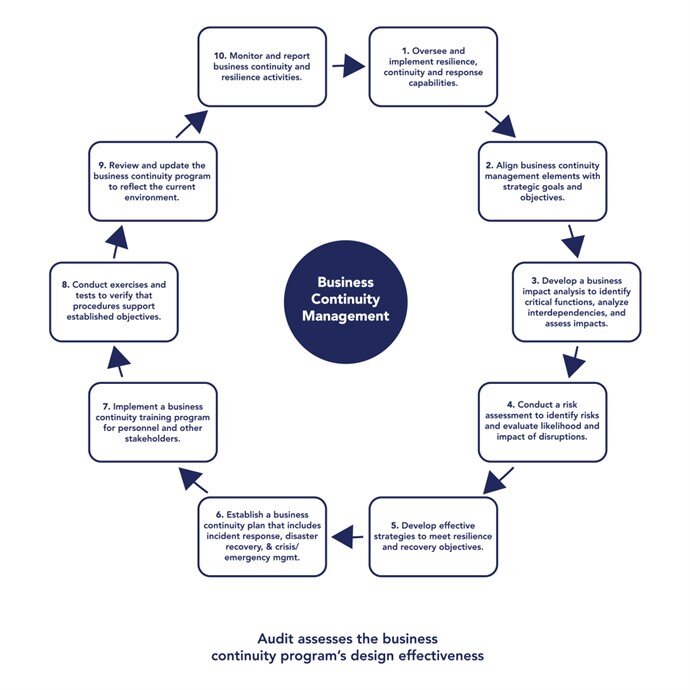
The second session delved into Microsoft 365’s robust security infrastructure, differentiating it from Office 365 by focusing on security, identity, and compliance. Our experts unraveled M365’s key security features—like Security Defaults, Global Auditing, and the reformation of mailbox protocols—and stressed best practices for managing these components. It highlighted the significance of applications, stopping user unauthorized trials or purchases, managing administrative roles, and ensuring secure email communications. It also provided a handy infographic to explore overlooked M365 security features to help you implement everything needed under your license type. Overall, this hands-on training demonstrated why keeping pace with such security measures is vital to preventing evolving cyber threats.
Part 3: Mastering Azure Tenant Configuration: CAPs and Intune Deployment
Azure, known for its expansive capabilities, demands meticulous configuration to leverage its potential fully. This session provided guidance on managing Azure/Entra ID tenants effectively, implementing CAPs, and deploying Intune. It covered essential aspects such as user-based exceptions for CAPs, Intune objectives, and tips for device and network maintenance. Attendees gained insights into crafting and enforcing policies that address unauthorized device access and ensure compliance with application usage, alongside strategies for regular device and policy maintenance to bolster their security.
Part 4: AI Governance and Accountability in Azure
Exploring the growing role of Artificial Intelligence (AI) in banking, this concluding session emphasized understanding governance and responsibility in deploying AI tools like Microsoft Copilot. It explained Copilot’s features and architecture, the importance of access control, and the implications of global data handling. With comprehensive insights, participants were shown how to balance innovation with security and compliance, maximizing data utility while safeguarding organizational integrity.
Watch All Four Sessions
These sessions provide security best practices and strategic insights into managing M365 environments effectively. Packed with practical demonstrations, expert advice, and interactive segments, the M365 Security Immersion Training is invaluable for financial institutions seeking to strengthen their security posture. Now you can access all recordings and tap into the wealth of knowledge this series offers.