It is important to understand your institution’s cybersecurity posture to find out where you stand in regard to cyber threats and what you need to do to create a more secure environment. It’s a delicate balance because being behind on your cybersecurity posture means your institution is less secure than it should be but being ahead likely means that you are investing in resources that you may not need. Unfortunately, it’s almost impossible to do a true peer-to-peer comparison because there are just too many variables between even similarly sized financial institutions to obtain a useful analysis. Here’s why:
Every Institution Has a Unique Model
When we implement information security or business continuity programs for banks and credit unions, we start with a process called “Enterprise Modeling” where we identify the departments, the processes, and the functions that make up each individual financial institution. What this process typically reveals is that if you model out two financial institutions that look identical in terms of geographic area, demographic customer or member base, size and complexity, the results will almost always be significantly different since each institution has a unique operating model based on their specific services, organization, processes, and technologies.
Cyber Risk Appetite Is a Key Variable
Cyber risk appetite is another factor that often differentiates your institution from your peers. Safe Systems’ Compliance Guru defines risk appetite as “The amount of risk that an enterprise is willing to pursue and accept in order to achieve the goals and objectives of their strategic plan.” For example, let’s say we have two financial institutions that seem equivalent in outward appearance. Based on their strategic plan, one institution has decided to take a more aggressive cybersecurity posture to electronic banking products and the other has decided to take a more conservative approach. Because the level of risk varies by the approach, you simply cannot accurately compare the two institutions.
The Best Way to Evaluate Cybersecurity Posture
At Safe Systems, we recommend allowing your bank or credit union’s information to stand on its own. To truly improve your cybersecurity posture, you must examine where you are based on where you need to be — not where a peer may be in the process. Carefully evaluate your risks (including areas of elevated risk), and the controls you have in place that offset those risks. Then, examine the best control groups to apply against those areas of elevated risk and develop an action plan to take your institution from where you are now, to where you need to be. Then, when you conduct this process again next year, you can demonstrate steady progress to both examiners and your Board.
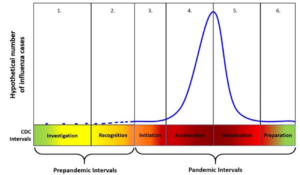
Holding Steady May Cause You to Fall Behind
In addition, just because your inherent risk profile isn’t increasing from one assessment to the next, this doesn’t necessarily mean your control maturity levels shouldn’t increase. The risk environment is constantly evolving, so holding steady on your controls may actually mean your cybersecurity resilience is decreasing. Making incremental increases in your control maturity levels will help keep you ahead of the latest threats.
For more information about improving your cybersecurity posture, watch the full “Banking Bits and Bytes Super Duper CEO Series,” below.