Our first Customer Success Summer Series offered live webinars with special guest speakers who shared their industry knowledge to help our customers and other financial institutions enhance internal processes and key areas of their banking operations.
- In August, we hosted Cary Parris, Co-Founder and CTO at iTransit Solutions who presented “The Evolution of Phone Systems: Which is Right for You?”.
- In September, we presented “2 Guys and a Microphone: Matt and Tom Chat About Compliance Trends and Rumors” where Matthew Jones, Partner and Financial and Information Security Auditor at Symphona, and Thomas Hinkel, the Compliance Guru at Safe Systems discussed recent developments and trends in regulations and shared their insights on current findings from examiners and auditors.
The Evolution of Phone Systems
Today businesses are facing the acceleration of remote working—Voice over internet protocol (VoIP), Virtual Private Networks (VPN), virtual meetings, and dynamic routing of phone systems based on the user’s location—all have become must-have requirements. Legacy telephone services are becoming more obsolete as some telecoms decommission analog technologies in favor of fiber pots and other alternatives. The old telephone system is evolving into a more modern option: unified communications as a service (UCaaS), which merges communication channels into a single cloud-based system. UCaaS offers all the necessary infrastructure, applications, and resources businesses need in an easily scalable solution. Unified communications tools can include chat, VoIP, text messaging, and online video conferencing.
UCaaS gives institutions the benefit of advanced functionality which allows employees to work remotely more efficiently, including things like the ability to check other users’ availability, reach people whether they are in the office or out in the field, and access the platform from anywhere. Another evolving facet in telecommunications is call center as a service (CCaaS), which also streamlines omnichannel communication and allows remote employees to work together as a call center team.
Given its flexibility and efficiency, it is easy to see why UCaaS is moving to the forefront of communications. There is a wide range of unified communications features, equipment, and prices and it is important for your institution to clearly define its unique needs to find a solution that will satisfy its requirements. It is also important to continue to evaluate your equipment and services every few years as technology and pricing continue to change.
Watch the recording of this webinar to gain a better understanding of UCaaS and other options so you can make the right choice for your institution.
2 Guys and a Microphone
Matt and Tom have both spent most of their careers focused on risk and regulatory compliance for financial institutions. We recorded their recent conversation which spans many topics including increased scrutiny on vendor management, continued focus on ransomware, and more.
Recent audit and exam trends continue to have a strong focus on third parties and proper vendor management. Examiners are considering the preponderance of fintechs, how much the average financial institution is outsourcing, and the inherent risk that originates from third-party vendors. Interestingly, their increased scrutiny may extend to any significant sub-service vendors that institutions may have. In addition, we are seeing questions arise about vendor management in the context of insurance. Cyber liability insurance applications are requesting more details about the management of vendors and other third parties.
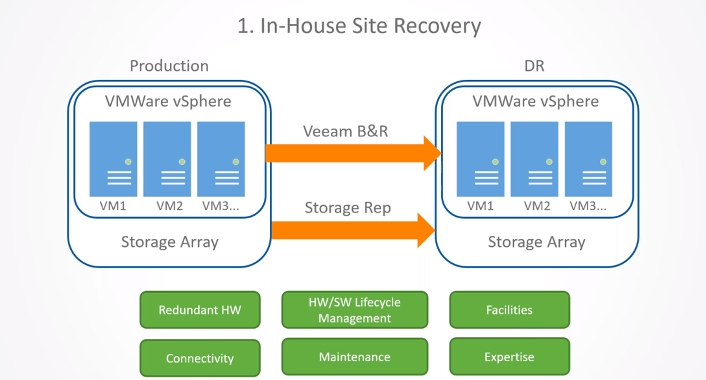
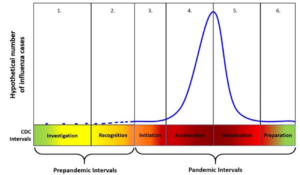
There have also been some interesting audit and exam findings. For instance, one institution was encouraged to complete a post-pandemic/walk-through test or “dry run” of their pandemic procedures. This is curious considering all institutions have been in a “live exercise” for the past few years with the pandemic. Regardless, there is a good chance that the pandemic verbiage in your disaster recovery plan needs to be updated based on what has or has not been done in response to the current pandemic. And it is important to consider that an annual pandemic test will be a part of examiner expectations going forward along with the traditional business continuity, natural disaster, and cyber incident tests.
On the regulatory front, the new Computer-Incident Notification Rule went into effect on April 1, 2022, which is designed to give regulators early awareness of emerging threats to banking organizations and the broader financial system, including potentially systemic cyber events. The rule has two components:
- The first part requires a banking organization to promptly notify its primary federal regulator of any “computer-security incident” that rises to the level of a “notification incident.”
- The second part requires a bank service provider to notify each affected banking organization customer as soon as possible when the bank service provider determines that it has experienced a “computer-security incident” that has caused, or is reasonably likely to cause, a material service disruption or degradation for four or more hours.
In March, we hosted an in-depth webinar on understanding the requirements, recognizing gray areas, and preparing for unknowns. To help intuitions meet these requirements, we also created a detailed flowchart to understand when an event is severe enough to activate your Incident Response Team (IRT) and when regulators and customers should be notified.
Another regulatory trend to keep your eyes on is the increasing focus on ransomware industry-wide is prompting some state banking organizations to require institutions to use the Ransomware Self-Assessment Tool (R-SAT). The 16-question R-SAT is designed to help institutions evaluate their general cybersecurity preparedness and reduce ransomware risks. The R-SAT supplements the Cybersecurity Assessment Tool developed by the Federal Financial Institutions Examination Council (FFIEC). It will be interesting to see if more states begin requiring this additional diagnostic tool.
Watch the recording to hear more insights about INTrex, SOC Reports, and SSAE 21.