The ISO’s role is becoming increasingly more complex and challenging due to growing cyber security threats, the ever-changing technology environment, and expanding regulatory expectations. It can be difficult for banks and credit unions to stay on top of information security issues. That’s why today even the smallest institutions often engage a trusted third party for help. A virtual information security officer (VISO) service can help institutions effectively manage information security so that nothing gets missed or falls through the cracks.
Common Types of VISO
The most common types of virtual ISO solutions available to institutions are the “do-it-yourself” (DIY), “hybrid,” and “offload” models. The DIY option is designed for institutions that have a solid grasp of the ISO’s job functions and just need some basic tools and limited consultation to enhance their efforts. This model is the least expensive but also requires more of a time commitment from your internal resources. The hybrid model may typically include an assortment of apps, templates, pre-configured reports, and other tools, along with a broader and deeper level of consultation. Resource requirements from the institution side are greatly reduced compared to DIY, but typically greater than offload. Accordingly, costs for a hybrid approach are somewhere between the two other models. The hybrid model also tends to be the most flexible and is designed to evolve with the changing needs of the institution. Finally, the offload approach attempts to provide a “turn-key” solution wherein the virtual ISO partner effectively assumes most or all the responsibilities of your internal ISO. This approach requires the least involvement from your institution (which could introduce other challenges…see the “Examiner Support” section below), but it is usually also the most expensive. As this model is the most inclusive, the knowledge and experience of the third-party provider are your most important consideration. The offload approach typically includes unlimited consultation, on-demand reporting, participation in committee meetings, etc.
Key Factors to Consider
When choosing a virtual ISO, there are some important aspects to consider to ensure your institution selects the best option. Keep in mind that each virtual ISO model comes with a certain level of flexibility and engagement for a specific price. The key is to carefully balance the service and costs against your specific internal resource gaps to determine the best solution for your situation. Ideally, whatever solution you choose should have the flexibility to dial up or down the level of service, depending on how your situation may change in the future.
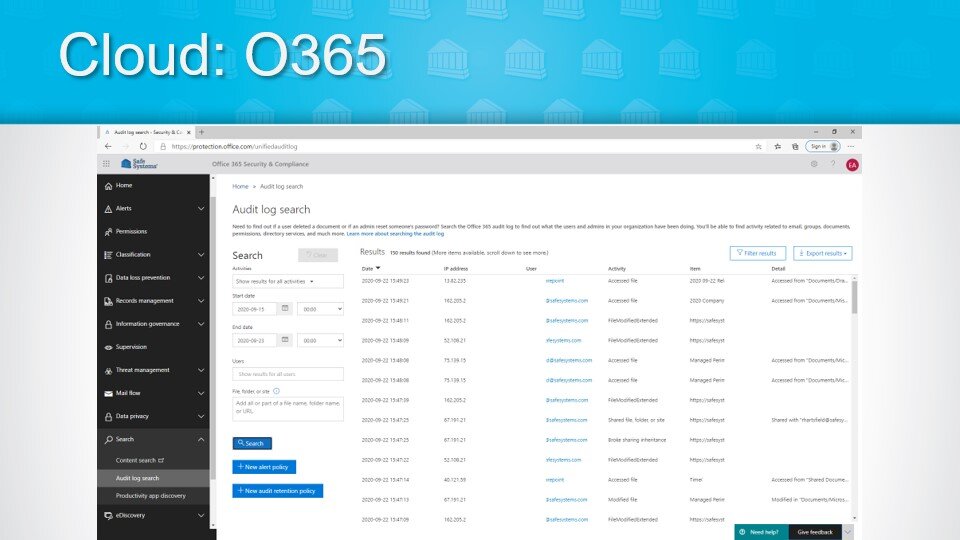
Whatever virtual ISO solution you opt for, it should provide documentation and reporting in a form that the various stakeholders can understand. Each one of the many ISO responsibilities has one or more reports or documents that support the requirement to hold the ISO accountable for its responsibilities. The board of directors, the steering committee, the IT auditors, and examiners, all have different perspectives and comprehension levels and may require different degrees of detail for the same information. For instance, boards and examiners might require higher-level data, whereas steering committees and IT auditors might require more detailed documentation for their purposes. You should have access to on-demand reporting with relevant, actionable, up-to-date information that matches the level of engagement for the various stakeholder groups.
The regulatory guidance on ISO responsibilities includes terms such as “engaging with” and “working with” management in the individual lines of business to understand the risks of various initiatives. They also expect the ISO to “implement” the information security strategy as defined by the board, and to periodically “inform” the board and senior management on the status of the program. In the case of a virtual ISO, your hybrid or offload third-party partner needs to have an excellent understanding of enterprise-wide strategic objectives, and a good working relationship with management in all lines of business and within the different departments within your organization.
Remember, as with all outsourced activities, even though you can delegate some (or even most) of the heavy lifting to a virtual ISO, you cannot outsource responsibility. Your institution still must maintain a strong oversight effort to ensure that all ISO duties are completed, documented, and reported appropriately. Higher levels of third-party reliance require correspondingly higher levels of oversight. According to the Federal Financial Institutions Examination Council’s Outsourcing Technology Services booklet you are obligated to oversee all activities, whether you perform them, or a third-party performs them on your behalf.
Examiner Support
The examiner feedback we have seen to date strongly supports the idea of financial institutions implementing a virtual ISO solution “…as long as it’s done correctly.” That means focusing on all the responsibilities and accountabilities of the role and making sure sufficient documentation and appropriate oversight and reporting are built-in. Doing it correctly also means making sure the in-house ISO is not so detached from the processes and procedures that they cannot authoritatively explain them to a stakeholder, which can be the primary downside of the “offload” model. The decision-making process is the most important concern for regulators. Your solution should allow you to offload enough to make the ISO’s job easier and more organized, but not so much that they become disconnected and lose operational awareness of their current threat and control environment.
In conclusion, choosing the right type of virtual ISO service allows institutions to provide the appropriate level of insight and oversight for their in-house ISO. This can help them to be better equipped to manage information security activities, meet evolving industry standards, and adjust to tightening regulatory requirements, all in an increasing cyber threat environment.
At Safe Systems, we offer a virtual ISO service based on the above-described hybrid model. ISOversight™, is a VISO service that is flexible to accommodate the changing needs of community banks and credit unions. The ISOversight service includes a full suite of applications to manage everything from vendors to business continuity, along with all associated information security policies and risk assessments. This is a cost-effective, comprehensive, and flexible solution that makes information security management much more efficient. For more insight about the most common virtual ISO models and how to determine which one may be right for you, view our webinar on “Is a Virtual ISO Right for You?”



























 Keith Haskett is the president and CEO of Rebyc Security and is responsible for executing their strategic plan. After several years leading the Risk and Information Security Consulting Services practice at CSI, he co-founded Rebyc to deliver offensive security solutions customized to meet the needs of the highly regulated, financial services industry. His teams have delivered over 2,000 engagements to financial institutions nationwide.
Keith Haskett is the president and CEO of Rebyc Security and is responsible for executing their strategic plan. After several years leading the Risk and Information Security Consulting Services practice at CSI, he co-founded Rebyc to deliver offensive security solutions customized to meet the needs of the highly regulated, financial services industry. His teams have delivered over 2,000 engagements to financial institutions nationwide.